---
title: Cloudflare bot solutions
description: While Cloudflare offers several products that relate to bot traffic, this section reviews our bot-specific products, Bot Fight Mode, Super Bot Fight Mode, and Bot Management for Enterprise.
image: https://developers.cloudflare.com/core-services-preview.png
---
[Skip to content](#%5Ftop)
Was this helpful?
YesNo
[ Edit page ](https://github.com/cloudflare/cloudflare-docs/edit/production/src/content/docs/bots/index.mdx) [ Report issue ](https://github.com/cloudflare/cloudflare-docs/issues/new/choose)
Copy page
# Cloudflare bot solutions
Identify and mitigate automated traffic to protect your domain from bad bots.
Available on all plans
While Cloudflare offers several products that relate to bot traffic, this section reviews our bot-specific products, Bot Fight Mode, Super Bot Fight Mode, and Bot Management for Enterprise.
Note
Enterprise customers can preview this product as a [non-contract service](https://developers.cloudflare.com/billing/preview-services/), which provides full access, free of metered usage fees, limits, and certain other restrictions.
## Which bot solution do I need?
If you have a smaller domain and have identified a bot problem, we recommend Bot Fight Mode or Super Bot Fight Mode, which are included with your plan subscription. You can enable either from your dashboard, but these solutions offer limited configuration options.
If you have a large domain with a lot of traffic, we recommend Bot Management for Enterprise, especially for customers in ecommerce, banking, and security. To enable Bot Management for Enterprise and write rules to customize your bot protection, contact your account team.
To see the differences in features and functionality, visit [Plans](https://developers.cloudflare.com/bots/plans/).
## Features
### Bot Fight Mode
Detect and mitigate bot traffic on your domain.
[ Use Bot Fight Mode ](https://developers.cloudflare.com/bots/get-started/bot-fight-mode/)
### Super Bot Fight Mode
Identify traffic matching patterns of known bots, challenge or block bots, protect static resources, and view analytics to help you understand bot traffic using Super Bot Fight Mode.
[ Use Super Bot Fight Mode ](https://developers.cloudflare.com/bots/get-started/super-bot-fight-mode/)
### Bot Analytics
Use Bot Analytics to dynamically examine bot traffic.
[ Use Bot Analytics ](https://developers.cloudflare.com/bots/bot-analytics/)
### Firewall variables
Access several new variables within the Firewall expression builder.
[ Use Firewall variables ](https://developers.cloudflare.com/bots/reference/bot-management-variables/)
## Related products
**[API Shield](https://developers.cloudflare.com/api-shield/)**
Identify and address API vulnerabilities using API Shield.
**[DDoS Protection](https://developers.cloudflare.com/ddos-protection/)**
Detect and mitigate Distributed Denial of Service (DDoS) attacks using Cloudflare's Autonomous Edge.
**[Turnstile](https://developers.cloudflare.com/turnstile/)**
Use Cloudflare's smart CAPTCHA alternative to run less intrusive challenges.
**[WAF](https://developers.cloudflare.com/waf/)**
Get automatic protection from vulnerabilities and the flexibility to create custom rules.
## More resources
[Plans](https://www.cloudflare.com/plans/#overview)
Compare available Cloudflare plans
```json
{"@context":"https://schema.org","@type":"BreadcrumbList","itemListElement":[{"@type":"ListItem","position":1,"item":{"@id":"/directory/","name":"Directory"}},{"@type":"ListItem","position":2,"item":{"@id":"/bots/","name":"Bots"}}]}
```
---
---
title: Plans
description: To learn more about features and functionality, select a plan.
image: https://developers.cloudflare.com/core-services-preview.png
---
[Skip to content](#%5Ftop)
Was this helpful?
YesNo
[ Edit page ](https://github.com/cloudflare/cloudflare-docs/edit/production/src/content/docs/bots/plans/index.mdx) [ Report issue ](https://github.com/cloudflare/cloudflare-docs/issues/new/choose)
Copy page
# Plans
To learn more about features and functionality, select a plan.
[ Free ](https://developers.cloudflare.com/bots/plans/free/) [ Pro ](https://developers.cloudflare.com/bots/plans/pro/) [ Business ](https://developers.cloudflare.com/bots/plans/biz-and-ent/) [ Bot Management for Enterprise ](https://developers.cloudflare.com/bots/plans/bm-subscription/)
## How do I get started?
To get started, review our [setup guides](https://developers.cloudflare.com/bots/get-started/). If you have any questions, visit the [community ↗](https://community.cloudflare.com/) to engage with other Cloudflare users.
```json
{"@context":"https://schema.org","@type":"BreadcrumbList","itemListElement":[{"@type":"ListItem","position":1,"item":{"@id":"/directory/","name":"Directory"}},{"@type":"ListItem","position":2,"item":{"@id":"/bots/","name":"Bots"}},{"@type":"ListItem","position":3,"item":{"@id":"/bots/plans/","name":"Plans"}}]}
```
---
---
title: Business
description: To learn more about features and functionality, select a plan.
image: https://developers.cloudflare.com/core-services-preview.png
---
[Skip to content](#%5Ftop)
Was this helpful?
YesNo
[ Edit page ](https://github.com/cloudflare/cloudflare-docs/edit/production/src/content/docs/bots/plans/biz-and-ent.mdx) [ Report issue ](https://github.com/cloudflare/cloudflare-docs/issues/new/choose)
Copy page
# Business
To learn more about features and functionality, select a plan.
[ Free ](https://developers.cloudflare.com/bots/plans/free/) [ Pro ](https://developers.cloudflare.com/bots/plans/pro/) [ Business ](https://developers.cloudflare.com/bots/plans/biz-and-ent/) [ Bot Management for Enterprise ](https://developers.cloudflare.com/bots/plans/bm-subscription/)
| **Plan name** | Super Bot Fight Mode |
| ------------------------- | ----------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------- |
| **Availability** | All Business customers and Enterprise customers without Bot Management[1](#user-content-fn-1) |
| **Type of bots detected** | Simple bots, headless browsers, and many sophisticated bots |
| **Actions** | Customer chooses whether to allow, block, or challenge |
| **Analytics** | Dedicated Bot Analytics tool, available in **Security Analytics** |
| **Control** | Applied to all traffic across a domain |
| **Additional features** | [Block AI bots](https://developers.cloudflare.com/bots/additional-configurations/block-ai-bots/), [AI Labyrinth](https://developers.cloudflare.com/bots/additional-configurations/ai-labyrinth/), [Instruct AI bot traffic with robots.txt](https://developers.cloudflare.com/bots/additional-configurations/managed-robots-txt/), [Definitely and Likely automated bots](https://developers.cloudflare.com/bots/concepts/bot-score/#bot-groupings), [Verified bots](https://developers.cloudflare.com/bots/concepts/bot/verified-bots/), [Static resource protection](https://developers.cloudflare.com/bots/additional-configurations/static-resources/), [Optimize for WordPress](https://developers.cloudflare.com/bots/troubleshooting/wordpress-loopback-issue/), [JavaScript Detections](https://developers.cloudflare.com/cloudflare-challenges/challenge-types/javascript-detections/) |
## Bot settings versus custom rules
The following features are handled automatically in **Security Settings** and do not require custom rules:
| Feature | Handled by bot settings | Requires custom rules |
| ----------------------------------------------- | ----------------------- | ----------------------------------------------------------------------------------------- |
| Block or challenge definitely automated traffic | Yes | Only for path-specific or threshold-tuned rules |
| Block or challenge likely automated traffic | Not available on Pro | Yes, with [Bot Management](https://developers.cloudflare.com/bots/plans/bm-subscription/) |
| Allow or block verified bots | Yes | No |
| Block AI crawlers | Yes | Only to target individual AI crawlers |
| Protect static resources | Yes | No |
| Optimize for WordPress | Yes | No |
For more details on when custom rules are needed, refer to [custom rules](https://developers.cloudflare.com/bots/additional-configurations/custom-rules/).
## How do I get started?
To get started, review our [setup guides](https://developers.cloudflare.com/bots/get-started/). If you have any questions, visit the [community ↗](https://community.cloudflare.com/) to engage with other Cloudflare users.
## Footnotes
1. When users purchase Bot Management for Enterprise, Cloudflare automatically replaces and disables other bot products to prevent overlap. [↩](#user-content-fnref-1)
```json
{"@context":"https://schema.org","@type":"BreadcrumbList","itemListElement":[{"@type":"ListItem","position":1,"item":{"@id":"/directory/","name":"Directory"}},{"@type":"ListItem","position":2,"item":{"@id":"/bots/","name":"Bots"}},{"@type":"ListItem","position":3,"item":{"@id":"/bots/plans/","name":"Plans"}},{"@type":"ListItem","position":4,"item":{"@id":"/bots/plans/biz-and-ent/","name":"Business"}}]}
```
---
---
title: Enterprise Bot Management
description: To learn more about features and functionality, select a plan.
image: https://developers.cloudflare.com/core-services-preview.png
---
[Skip to content](#%5Ftop)
Was this helpful?
YesNo
[ Edit page ](https://github.com/cloudflare/cloudflare-docs/edit/production/src/content/docs/bots/plans/bm-subscription.mdx) [ Report issue ](https://github.com/cloudflare/cloudflare-docs/issues/new/choose)
Copy page
# Enterprise Bot Management
To learn more about features and functionality, select a plan.
[ Free ](https://developers.cloudflare.com/bots/plans/free/) [ Pro ](https://developers.cloudflare.com/bots/plans/pro/) [ Business ](https://developers.cloudflare.com/bots/plans/biz-and-ent/) [ Bot Management for Enterprise ](https://developers.cloudflare.com/bots/plans/bm-subscription/)
| **Plan name** | Bot Management for Enterprise |
| ------------------------- | ----------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------- |
| **Availability** | Added to Enterprise plans by your account team |
| **Enablement** | Quick onboarding with help from our Solutions Engineering team |
| **Type of bots detected** | Simple and sophisticated bots, headless browsers, and domain-specific anomalies |
| **Actions** | Customer chooses from several options, including block and various challenges |
| **Analytics** | Dedicated Bot Analytics tool, available in **Security Analytics** |
| **Control** | Ability to restrict by path, IP address, and more. Access to [bot score](https://developers.cloudflare.com/bots/concepts/bot-score/), [JA3/JA4 fingerprint](https://developers.cloudflare.com/bots/additional-configurations/ja3-ja4-fingerprint/), [bot tags](https://developers.cloudflare.com/bots/concepts/bot-tags/) fields, and [detection IDs](https://developers.cloudflare.com/bots/additional-configurations/detection-ids/). |
| **Additional features** | [Block AI bots](https://developers.cloudflare.com/bots/additional-configurations/block-ai-bots/), [AI Labyrinth](https://developers.cloudflare.com/bots/additional-configurations/ai-labyrinth/), [Instruct AI bot traffic with robots.txt](https://developers.cloudflare.com/bots/additional-configurations/managed-robots-txt/), [Definitely and Likely automated bots](https://developers.cloudflare.com/bots/concepts/bot-score/#bot-groupings), [Verified bots](https://developers.cloudflare.com/bots/concepts/bot/verified-bots/), [Static resource protection](https://developers.cloudflare.com/bots/additional-configurations/static-resources/), [Optimize for WordPress](https://developers.cloudflare.com/bots/troubleshooting/wordpress-loopback-issue/), [JavaScript Detections](https://developers.cloudflare.com/cloudflare-challenges/challenge-types/javascript-detections/) |
Note
Zones that have [Enterprise Bot Management](https://developers.cloudflare.com/bots/get-started/bot-management/) enabled will not see Bot Fight Mode or Super Bot Fight Mode under **Security** \> **Bots**.
## Bot settings vs. custom rules
Bot Management customers have both bot settings (configured in **Security Settings**) and the ability to create custom rules using bot score fields. Start with the bot settings for baseline protection, then add custom rules only when you need additional control.
| Feature | Handled by bot settings | When to use custom rules instead |
| ----------------------------------------------- | ----------------------- | ------------------------------------------------------------------------------------------------------------------------------------------ |
| Block or challenge definitely automated traffic | No | Path-specific rules, custom thresholds, or combining with other fields |
| Block or challenge likely automated traffic | No | Path-specific rules, custom thresholds, or combining with other fields |
| Allow or block verified bots | No | Granular control by verified bot category |
| Block AI crawlers | Yes | Target individual AI crawlers using detection IDs |
| Protect static resources | No | Exclude static resources from specific rules |
| Optimize for WordPress | No | No |
| Forward bot data to origin | No | Use [Transform Rules](https://developers.cloudflare.com/rules/transform/) or [Snippets](https://developers.cloudflare.com/rules/snippets/) |
| Detection ID targeting | No | Use cf.bot\_management.detection\_ids in [custom rules](https://developers.cloudflare.com/waf/custom-rules/) |
| JA3/JA4 fingerprint rules | No | Use cf.bot\_management.ja3\_hash or cf.bot\_management.ja4 in [custom rules](https://developers.cloudflare.com/waf/custom-rules/) |
For more details on when custom rules are needed, refer to [custom rules](https://developers.cloudflare.com/bots/additional-configurations/custom-rules/).
## How do I get started?
To get started, review our [setup guides](https://developers.cloudflare.com/bots/get-started/). If you have any questions, visit the [community ↗](https://community.cloudflare.com/) to engage with other Cloudflare users.
```json
{"@context":"https://schema.org","@type":"BreadcrumbList","itemListElement":[{"@type":"ListItem","position":1,"item":{"@id":"/directory/","name":"Directory"}},{"@type":"ListItem","position":2,"item":{"@id":"/bots/","name":"Bots"}},{"@type":"ListItem","position":3,"item":{"@id":"/bots/plans/","name":"Plans"}},{"@type":"ListItem","position":4,"item":{"@id":"/bots/plans/bm-subscription/","name":"Enterprise Bot Management"}}]}
```
---
---
title: Free
description: To learn more about features and functionality, select a plan.
image: https://developers.cloudflare.com/core-services-preview.png
---
[Skip to content](#%5Ftop)
Was this helpful?
YesNo
[ Edit page ](https://github.com/cloudflare/cloudflare-docs/edit/production/src/content/docs/bots/plans/free.mdx) [ Report issue ](https://github.com/cloudflare/cloudflare-docs/issues/new/choose)
Copy page
# Free
To learn more about features and functionality, select a plan.
[ Free ](https://developers.cloudflare.com/bots/plans/free/) [ Pro ](https://developers.cloudflare.com/bots/plans/pro/) [ Business ](https://developers.cloudflare.com/bots/plans/biz-and-ent/) [ Bot Management for Enterprise ](https://developers.cloudflare.com/bots/plans/bm-subscription/)
| **Plan name** | Bot Fight Mode |
| ------------------------- | --------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------- |
| **Availability** | All Free customers |
| **Type of bots detected** | Simple bots (from cloud ASNs) and headless browsers |
| **Actions** | Cloudflare issues a computationally expensive challenge |
| **Control** | Applied to all traffic across a domain |
| **Additional features** | [Block AI bots](https://developers.cloudflare.com/bots/additional-configurations/block-ai-bots/), [AI Labyrinth](https://developers.cloudflare.com/bots/additional-configurations/ai-labyrinth/), [Instruct AI bot traffic with robots.txt](https://developers.cloudflare.com/bots/additional-configurations/managed-robots-txt/) |
## How do I get started?
To get started, review our [setup guides](https://developers.cloudflare.com/bots/get-started/). If you have any questions, visit the [community ↗](https://community.cloudflare.com/) to engage with other Cloudflare users.
```json
{"@context":"https://schema.org","@type":"BreadcrumbList","itemListElement":[{"@type":"ListItem","position":1,"item":{"@id":"/directory/","name":"Directory"}},{"@type":"ListItem","position":2,"item":{"@id":"/bots/","name":"Bots"}},{"@type":"ListItem","position":3,"item":{"@id":"/bots/plans/","name":"Plans"}},{"@type":"ListItem","position":4,"item":{"@id":"/bots/plans/free/","name":"Free"}}]}
```
---
---
title: Pro
description: To learn more about features and functionality, select a plan.
image: https://developers.cloudflare.com/core-services-preview.png
---
[Skip to content](#%5Ftop)
Was this helpful?
YesNo
[ Edit page ](https://github.com/cloudflare/cloudflare-docs/edit/production/src/content/docs/bots/plans/pro.mdx) [ Report issue ](https://github.com/cloudflare/cloudflare-docs/issues/new/choose)
Copy page
# Pro
To learn more about features and functionality, select a plan.
[ Free ](https://developers.cloudflare.com/bots/plans/free/) [ Pro ](https://developers.cloudflare.com/bots/plans/pro/) [ Business ](https://developers.cloudflare.com/bots/plans/biz-and-ent/) [ Bot Management for Enterprise ](https://developers.cloudflare.com/bots/plans/bm-subscription/)
| **Plan name** | Super Bot Fight Mode |
| ------------------------- | ------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------ |
| **Availability** | All Pro customers |
| **Type of bots detected** | Simple bots and headless browsers |
| **Actions** | Customer chooses whether to allow, block, or challenge |
| **Analytics** | Limited analytics available in a **Bot Report** |
| **Control** | Applied to all traffic across a domain |
| **Additional features** | [Block AI bots](https://developers.cloudflare.com/bots/additional-configurations/block-ai-bots/), [AI Labyrinth](https://developers.cloudflare.com/bots/additional-configurations/ai-labyrinth/), [Instruct AI bot traffic with robots.txt](https://developers.cloudflare.com/bots/additional-configurations/managed-robots-txt/), [Definitely automated bots](https://developers.cloudflare.com/bots/concepts/bot-score/#bot-groupings), [Verified bots](https://developers.cloudflare.com/bots/concepts/bot/verified-bots/), [Static resource protection](https://developers.cloudflare.com/bots/additional-configurations/static-resources/), [Optimize for WordPress](https://developers.cloudflare.com/bots/troubleshooting/wordpress-loopback-issue/), [JavaScript Detections](https://developers.cloudflare.com/cloudflare-challenges/challenge-types/javascript-detections/) |
## Bot settings versus custom rules
The following features are handled automatically in **Security Settings** and do not require custom rules:
| Feature | Handled by bot settings | Requires custom rules |
| ----------------------------------------------- | ----------------------- | ----------------------------------------------------------------------------------------- |
| Block or challenge definitely automated traffic | Yes | Only for path-specific or threshold-tuned rules |
| Block or challenge likely automated traffic | Not available on Pro | Yes, with [Bot Management](https://developers.cloudflare.com/bots/plans/bm-subscription/) |
| Allow or block verified bots | Yes | No |
| Block AI crawlers | Yes | Only to target individual AI crawlers |
| Protect static resources | Yes | No |
| Optimize for WordPress | Yes | No |
For more details on when custom rules are needed, refer to [custom rules](https://developers.cloudflare.com/bots/additional-configurations/custom-rules/).
## How do I get started?
To get started, review our [setup guides](https://developers.cloudflare.com/bots/get-started/). If you have any questions, visit the [community ↗](https://community.cloudflare.com/) to engage with other Cloudflare users.
```json
{"@context":"https://schema.org","@type":"BreadcrumbList","itemListElement":[{"@type":"ListItem","position":1,"item":{"@id":"/directory/","name":"Directory"}},{"@type":"ListItem","position":2,"item":{"@id":"/bots/","name":"Bots"}},{"@type":"ListItem","position":3,"item":{"@id":"/bots/plans/","name":"Plans"}},{"@type":"ListItem","position":4,"item":{"@id":"/bots/plans/pro/","name":"Pro"}}]}
```
---
---
title: Bot Analytics
description: Business and Enterprise customers without Bot Management can use Bot Analytics to dynamically examine bot traffic. These dashboards offer less functionality than Bot Management for Enterprise but still help you understand bot traffic on your domain.
image: https://developers.cloudflare.com/core-services-preview.png
---
[Skip to content](#%5Ftop)
Was this helpful?
YesNo
[ Edit page ](https://github.com/cloudflare/cloudflare-docs/edit/production/src/content/docs/bots/bot-analytics.mdx) [ Report issue ](https://github.com/cloudflare/cloudflare-docs/issues/new/choose)
Copy page
# Bot Analytics
## Business and Enterprise
Business and Enterprise customers without Bot Management can use **Bot Analytics** to dynamically examine bot traffic. These dashboards offer less functionality than Bot Management for Enterprise but still help you understand bot traffic on your domain.
### Access
You can access Bot Analytics by going to the [Cloudflare dashboard ↗](https://dash.cloudflare.com/login), and selecting your account and domain.
Old dashboard: **Security** \> **Bots**.
New dashboard: **Security** \> **Analytics** \> **Bot analysis**.
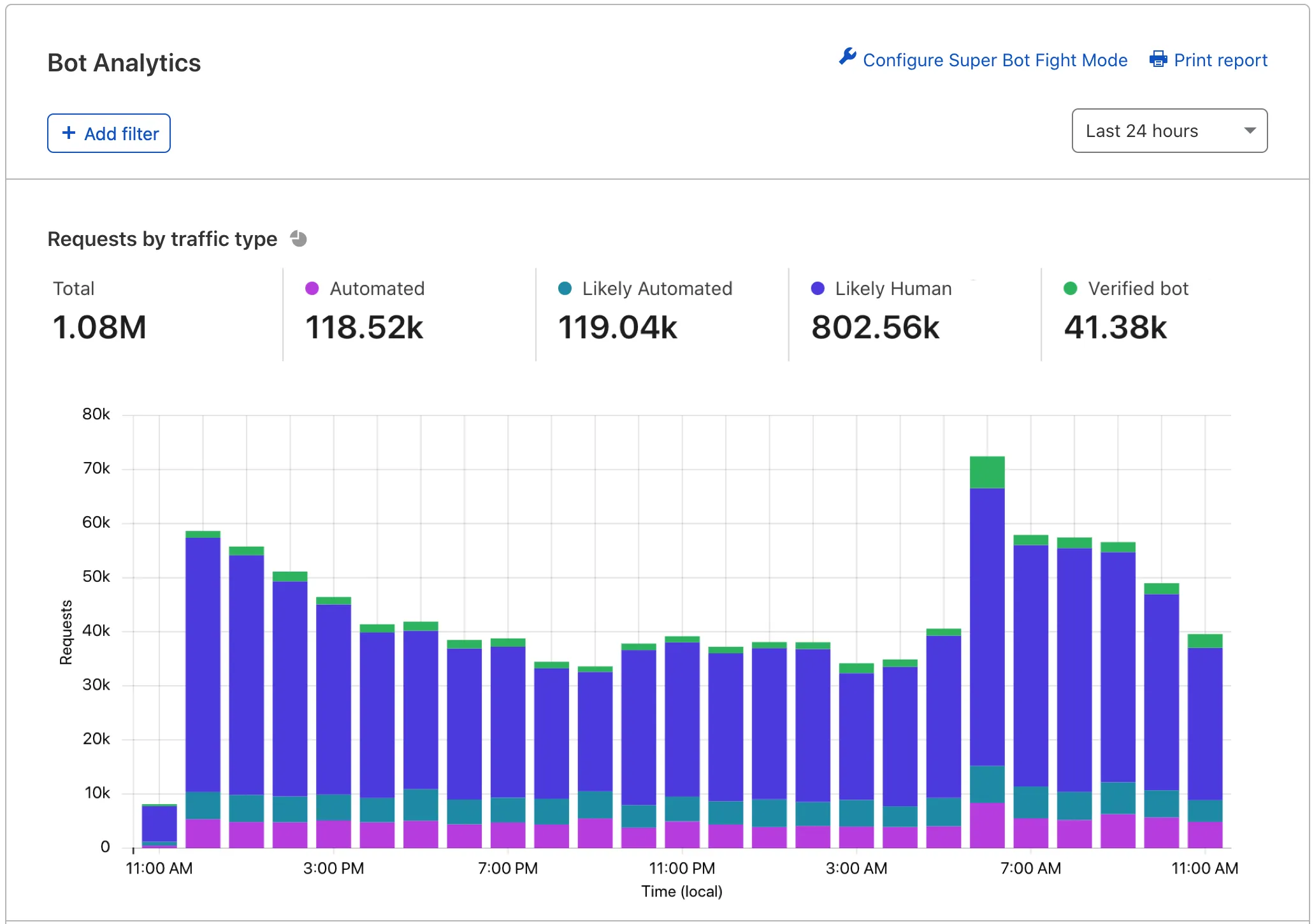
### Features
For a full tour of Bot Analytics, see [our blog post ↗](https://blog.cloudflare.com/introducing-bot-analytics/). At a high level, the tool includes:
* **Requests by traffic type**: View your total domain traffic segmented vertically by traffic type. Keep an eye on _automated_ and _likely automated_ traffic.
* **Requests by detection source**: Identify the most common detection engines used to score your traffic. Hover over a tooltip to learn more about each engine.
* **Top requests by attribute**: View more detailed information on specific IP addresses and other characteristics.
Bot Analytics shows up to 72 hours of data at a time and can display data up to 30 days old. Bot Analytics displays data in real time in most cases.
Cloudflare uses adaptive bitrate technology to show sampled data — most customers will see a 1-10% sample depending on how much information they are trying to view. Tooltips on the page will display the current sample rate.
### Common uses
Business and Enterprise customers without Bot Management can use Bot Analytics to:
* Understand bot traffic
* Study recent attacks to find trends and detailed information
* Learn more about Cloudflare’s detection engines with real data
For more details and granular control over bot traffic, consider upgrading to [Bot Management for Enterprise](https://developers.cloudflare.com/bots/bot-analytics/#enterprise-bot-management).
## Enterprise Bot Management
Enterprise customers with Bot Management can use **Bot Analytics** to dynamically examine bot traffic.
### Access
You can access Bot Analytics by going to the [Cloudflare dashboard ↗](https://dash.cloudflare.com/login), and selecting your account and domain.
Old dashboard: **Security** \> **Bots**.
New dashboard: **Security** \> **Analytics** \> **Bot analysis**.
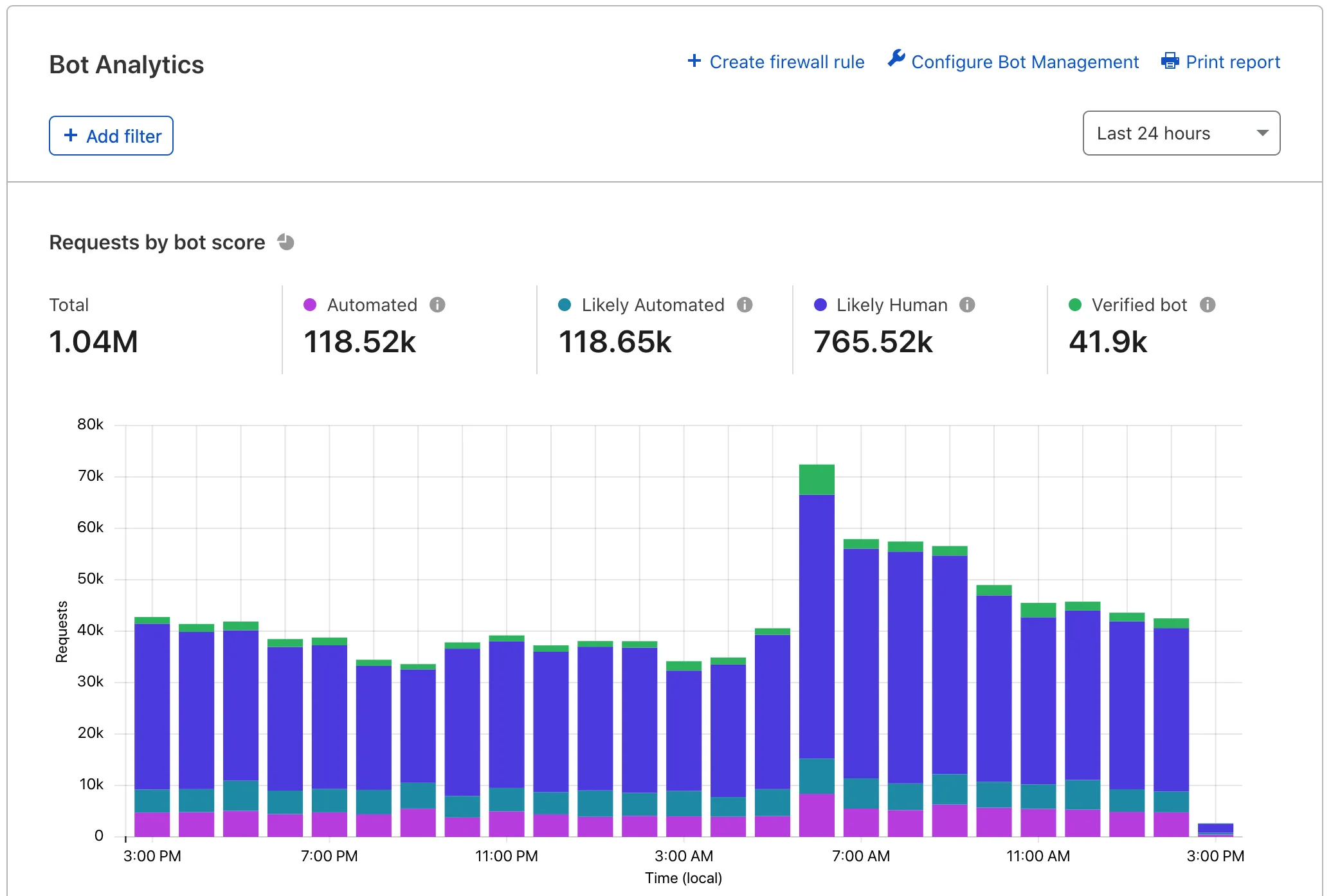
### Features
For a full tour of Bot Analytics, see [our blog post ↗](https://blog.cloudflare.com/introducing-bot-analytics/). At a high level, the tool includes:
* **Requests by bot score**: View your total domain traffic and segment it vertically by traffic type. Keep an eye on _automated_ and _likely automated_ traffic.
* **Bot score distribution**: View the number of requests assigned a bot score 1 through 99.
* **Bot score source**: Identify the most common detection engines used to score your traffic. Hover over a tooltip to learn more about each engine.
* **Top requests by attribute**: View more detailed information on specific IP addresses and other characteristics.
Bot Analytics shows up to one week of data at a time and can display data up to 30 days old. Bot Analytics displays data in real time in most cases.
Cloudflare uses adaptive bitrate technology to show sampled data — most customers will see a 1-10% sample depending on how much information they are trying to view. Tooltips on the page will display the current sample rate.
### Common uses
Bot Management customers can use Bot Analytics to:
* Understand traffic during [your onboarding phase](https://developers.cloudflare.com/bots/get-started/bot-management/).
* Tune WAF custom rules to be effective but not overly aggressive.
* Study recent attacks to find trends and detailed information.
* Learn more about Cloudflare’s detection engines with real data.
### API
Data from Bot Analytics is also available via the GraphQL API. You can access bot scores, bot sources, [bot tags](https://developers.cloudflare.com/bots/concepts/bot-tags/), and bot _decisions_ (_automated_, _likely automated_, etc.), and more.
Read the [GraphQL Analytics API documentation](https://developers.cloudflare.com/analytics/graphql-api/) for more information about GraphQL and basic querying.
```json
{"@context":"https://schema.org","@type":"BreadcrumbList","itemListElement":[{"@type":"ListItem","position":1,"item":{"@id":"/directory/","name":"Directory"}},{"@type":"ListItem","position":2,"item":{"@id":"/bots/","name":"Bots"}},{"@type":"ListItem","position":3,"item":{"@id":"/bots/bot-analytics/","name":"Bot Analytics"}}]}
```
---
---
title: Account Abuse Protection (Early Access)
description: Fraud detection allows you to detect and mitigate account abuse among your traffic, specifically bulk account creation and account takeover attacks. You can use fraud signals to update or create new rules for suspicious account activity, or pass signals to their origins to integrate into authentication and authorization systems.
image: https://developers.cloudflare.com/core-services-preview.png
---
[Skip to content](#%5Ftop)
Was this helpful?
YesNo
[ Edit page ](https://github.com/cloudflare/cloudflare-docs/edit/production/src/content/docs/bots/account-abuse-protection.mdx) [ Report issue ](https://github.com/cloudflare/cloudflare-docs/issues/new/choose)
Copy page
# Account Abuse Protection (Early Access)
Identify and mitigate attacks on your customer and user accounts.
Fraud detection allows you to detect and mitigate account abuse among your traffic, specifically bulk account creation and account takeover attacks. You can use fraud signals to [update or create new rules](https://developers.cloudflare.com/waf/custom-rules/) for suspicious account activity, or pass signals to their origins to integrate into authentication and authorization systems.
## Availability
Account Abuse Protection is available in Early Access for any [Bot Management Enterprise](https://developers.cloudflare.com/bots/get-started/bot-management) customer. You can use these features at no additional cost for a limited period until they are generally available.
Contact your Cloudflare account team to request access.
---
## Concepts
### User ID
User ID is a cryptographically hashed, per-zone identifier that customers can use in [Security Analytics](https://developers.cloudflare.com/waf/analytics/security-analytics/), [Security Rules](https://developers.cloudflare.com/waf/custom-rules/), and [Managed Transforms](https://developers.cloudflare.com/rules/transform/managed-transforms/reference/). With access to hashed User ID, website owners can:
* Review which users have the most activity on your website.
* Find the details on a specific user's characteristics and activity patterns.
* Mitigate traffic based on the user, such as blocking a user with historically suspicious activity.
* Combine fields to see when accounts are being targeted with leaked credentials.
* Manage network patterns or signals associated with specific users.
Data privacy
User profiling was created with privacy in mind. Its design and engineering align with our privacy and compliance programs and contain technical controls that protect the privacy of users. Hashed User IDs are created by encrypting the primary credentials your users use to access your applications.
Other Cloudflare customers cannot access your user profiles. They are unique to your zone.
User ID is enabled by default in the Cloudflare dashboard.
To edit or disable the setting:
1. In the Cloudflare dashboard, go to the **Security Settings** page.
[ Go to **Settings** ](https://dash.cloudflare.com/?to=/:account/:zone/security/settings)
2. Filter by **Fraud**.
3. Go to **User ID**.
4. Turn **User ID** on or off.
### Ephemeral IDs
Customers using Cloudflare [Turnstile](https://developers.cloudflare.com/turnstile/) can utilize ephemeral IDs for Fraud detection.
Refer to [Fraud detection with ephemeral IDs](https://developers.cloudflare.com/turnstile/tutorials/fraud-detection-with-ephemeral-ids/) for more information.
### Account takeover detections
Cloudflare Bot Management includes dedicated detection IDs for account takeover attacks.
Refer to [Account takeover detections](https://developers.cloudflare.com/bots/additional-configurations/detection-ids/account-takeover-detections/) for more information.
---
## Get started
### Prerequisites
Fraud detection requires the following configurations and settings to be enabled to properly identify suspicious behavior.
#### Security Settings
* User ID: Cloudflare encrypts or hashes your user IDs to better understand typical user traffic patterns across your applications. Enabling Cloudflare to create hashed user ID mappings to your users will allow you to receive account takeover and bulk account creation detections.
#### Eligible traffic
Cloudflare automatically identifies certain login and sign up traffic on your applications and runs these detections without any additional configurations.
* Sign-ups: Cloudflare automatically monitors traffic on endpoints that match common sign up endpoints.
* Login: Cloudflare automatically monitors traffic on endpoints that match common login endpoints.
Verify that your endpoints are properly labeled to ensure Cloudflare can detect and monitor them correctly.
Login or sign up endpoints
Not all login or sign up endpoints are automatically detected.
Cloudflare evaluates and automatically detects your website or application's login or sign up endpoint, but non-traditional login or sign up endpoints may not be recognized.
For example, if you have a non-traditional login endpoint, you should label it with `cf-log-in` using the [endpoint labeling service](https://developers.cloudflare.com/api-shield/management-and-monitoring/endpoint-labels/). Once you have applied the `cf-log-in` label, Cloudflare will use the labeled endpoint for account takeover detection decisions.
Enhanced with leaked credential detections
Cloudflare also recommends enabling [Leaked credentials detection](https://developers.cloudflare.com/waf/detections/leaked-credentials/) to help identify compromised credentials across your users.
---
### Detections
Fraud detections focus on account abuse attacks such as account takeover, bulk account creation, and credential quality. These detections run on all eligible traffic and can be used across [Cloudflare Rules](https://developers.cloudflare.com/rules/) to log, challenge, and/or block requests to your sign up and login endpoints.
#### Account creation
Disposable Email Checks detect when users sign up with throwaway email addresses commonly used for promotion abuse and fake account creation. These disposable email services allow attackers to create thousands of unique accounts without maintaining real infrastructure.
You can use the following binary field as you build rules to enforce security preferences, choosing to block all disposable emails outright, or issue a [challenge](https://developers.cloudflare.com/cloudflare-challenges/challenge-types/) to anyone attempting to create an account with a disposable email.
#### Suspicious emails
Cloudflare analyzes the components of an email used during sign up to help identify suspicious patterns. Refer to [prerequisites](#prerequisites) to ensure your traffic is eligible for detections.
Cloudflare does not store email addresses during this analysis. All detections processed without any storage or caching.
| Detection tag | Description |
| ------------------------------------- | --------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------- |
| cf.fraud\_detection.disposable\_email | Identifies emails with domains that are commonly found in lists of temporary or disposable email services. |
| cf.fraud.email\_risk | Analyzes the randomness of characters in an email username and top level domain. High risk emails indicate high entropy, while medium and low risk emails indicate less randomness in the string of characters. |
---
### Mitigations
The following Fraud detection fields can be used in Security Rules to help identify and mitigate suspicious traffic.
#### Security Rules
The following fields can be used in new and existing Security Rules.
| Field | Description | Values |
| -------------------------------------- | -------------------------------------------------------------------------------------------------- | ----------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------- |
| cf.fraud\_detection.disposable\_domain | Flags whether a domain for a given email is included in a known list of temporary email providers. | True or False |
| cf.fraud.email\_risk | Measures risk of email based on randomness of characters in the username and domain. | Low represents low risk due to reduced randomness and simple emails. Medium represents medium risk based on larger strings with slightly more randomness. High represents high risk based on larger and random character strings. Unknown |
#### Other rules
You can use Fraud detection data in Request Header [Transform Rules](https://developers.cloudflare.com/rules/transform/managed-transforms/) to pass information down to the origin.
#### LogPush
You can add Fraud detection fields to existing or new [LogPush](https://developers.cloudflare.com/logs/logpush/) jobs.
---
## Analytics
You can find Fraud data and detections in Security Analytics, where you can see top User IDs.
[ Go to **Analytics** ](https://dash.cloudflare.com/?to=/:account/:zone/security/analytics)
Fraud fields can be used as filters to identify suspicious patterns in your traffic.
The hashed User ID field within Security Analytics also provides Fraud customers with data that can help review detections and patterns per individual users rather than requests. You can review user level aggregations for IPs and IP counts, event types (login or sign up), locations, devices, and browsers.
A user level profile also provides a quick way to review the latest events associated with a user so that you can identify any anomalies and create a custom rule to log, block, or challenge that user.
```json
{"@context":"https://schema.org","@type":"BreadcrumbList","itemListElement":[{"@type":"ListItem","position":1,"item":{"@id":"/directory/","name":"Directory"}},{"@type":"ListItem","position":2,"item":{"@id":"/bots/","name":"Bots"}},{"@type":"ListItem","position":3,"item":{"@id":"/bots/account-abuse-protection/","name":"Account Abuse Protection (Early Access)"}}]}
```
---
---
title: Glossary
description: Review the definitions for terms used across Cloudflare's Bots documentation.
image: https://developers.cloudflare.com/core-services-preview.png
---
[Skip to content](#%5Ftop)
Was this helpful?
YesNo
[ Edit page ](https://github.com/cloudflare/cloudflare-docs/edit/production/src/content/docs/bots/glossary.mdx) [ Report issue ](https://github.com/cloudflare/cloudflare-docs/issues/new/choose)
Copy page
# Glossary
Review the definitions for terms used across Cloudflare's Bots documentation.
| Term | Definition |
| -------------------------- | ---------------------------------------------------------------------------------------------------------------------------------------------------------------------------- |
| bot | A software application programmed to do tasks that can be used for good (chatbots, search engine crawlers) or for evil (inventory hoarding, credential stuffing). |
| bot score | A score from 1 to 99 that indicates how likely that request came from a bot, in which 1 to 29 is likely automated and 30 to 99 is likely human. |
| bot tags | Additional information about a bot request, such as why Cloudflare has given it a bot score and whether the request came from a verified bot or a category of verified bots. |
| Challenge solve rate (CSR) | The percentage of issued challenges that were solved. |
| detection ID | Static rules that are used to detect predictable bot behavior with no overlap with human traffic. |
| JA3 fingerprint | JA3 and JA4 fingerprints profile specific SSL/TLS clients across different destination IPs, Ports, and X509 certificates. |
| verified bot | Bots that are transparent about who they are and what they do. |
```json
{"@context":"https://schema.org","@type":"BreadcrumbList","itemListElement":[{"@type":"ListItem","position":1,"item":{"@id":"/directory/","name":"Directory"}},{"@type":"ListItem","position":2,"item":{"@id":"/bots/","name":"Bots"}},{"@type":"ListItem","position":3,"item":{"@id":"/bots/glossary/","name":"Glossary"}}]}
```
---
---
title: Changelog
description: Subscribe to RSS
image: https://developers.cloudflare.com/core-services-preview.png
---
[Skip to content](#%5Ftop)
Was this helpful?
YesNo
[ Edit page ](https://github.com/cloudflare/cloudflare-docs/edit/production/src/content/docs/bots/changelog.mdx) [ Report issue ](https://github.com/cloudflare/cloudflare-docs/issues/new/choose)
Copy page
# Changelog
[ Subscribe to RSS ](https://developers.cloudflare.com/bots/changelog/index.xml)
## 2025-07-02
**Managed robots.txt will prepend existing files**
Cloudflare will prepend our managed `robots.txt` before your existing `robots.txt`, combining both into a single response.
## 2025-06-26
**Web Bot Auth is now available for bot verification**
Web Bot Auth is an authentication method that leverages cryptographic signatures in HTTP messages to verify that a request comes from an automated bot. This provides a more robust way of verifying bots.
## 2025-05-14
**Anomaly detection events now receive a bot score of 2**
Events detected by the [anomaly detection engine](https://developers.cloudflare.com/bots/concepts/bot-detection-engines/#anomaly-detection-enterprise) are now given a bot score of 2.
## 2025-05-08
**Machine Learning model v9 is now the default model**
[Machine Learning model v9](https://developers.cloudflare.com/bots/reference/machine-learning-models/#model-versions-and-release-notes) is now the default model for all new zones and existing zones set to use the latest machine learning model.
## 2025-04-28
**Managed robots.txt is now available**
Direct AI crawlers on what they can and cannot scrape from your website or application by [implementing a robots.txt file](https://developers.cloudflare.com/bots/additional-configurations/managed-robots-txt/) to your domain.
## 2025-04-24
**Bot Detection Alerts are now available**
You can now create a [Bot Detection Alert](https://developers.cloudflare.com/bots/reference/alerts/) to notify you when Cloudflare detects a spike in Bot traffic on your website.
## 2024-08-19
**AI bots is now a managed rule**
[AI bots protection](https://developers.cloudflare.com/bots/concepts/bot/#ai-bots) has been upgraded from a custom rule to a managed rule.
```json
{"@context":"https://schema.org","@type":"BreadcrumbList","itemListElement":[{"@type":"ListItem","position":1,"item":{"@id":"/directory/","name":"Directory"}},{"@type":"ListItem","position":2,"item":{"@id":"/bots/","name":"Bots"}},{"@type":"ListItem","position":3,"item":{"@id":"/bots/changelog/","name":"Changelog"}}]}
```
---
---
title: AI Labyrinth
description: The AI Labyrinth adds invisible links on your webpage with specific Nofollow tags to block AI crawlers that do not adhere to the recommended guidelines and crawl without permission. AI crawlers that scrape your website content without permission will be stuck in a maze of never-ending links, and their details are recorded and used by all Cloudflare customers who choose to block AI bots.
image: https://developers.cloudflare.com/core-services-preview.png
---
[Skip to content](#%5Ftop)
### Tags
[ AI ](https://developers.cloudflare.com/search/?tags=AI)
Was this helpful?
YesNo
[ Edit page ](https://github.com/cloudflare/cloudflare-docs/edit/production/src/content/docs/bots/additional-configurations/ai-labyrinth.mdx) [ Report issue ](https://github.com/cloudflare/cloudflare-docs/issues/new/choose)
Copy page
# AI Labyrinth
The AI Labyrinth adds invisible links on your webpage with specific `Nofollow` tags to block AI crawlers that do not adhere to the recommended guidelines and crawl without permission. AI crawlers that scrape your website content without permission will be stuck in a maze of never-ending links, and their details are recorded and used by all Cloudflare customers who choose to block [AI bots](https://developers.cloudflare.com/bots/concepts/bot/#ai-bots).
These links do not impact your search engine optimization (SEO) or your website's appearance, and are only seen by bots. AI bots that respect no-crawl instructions will safely ignore this honeypot.
To enable [AI Labyrinth](https://developers.cloudflare.com/bots/additional-configurations/ai-labyrinth):
* [ New dashboard ](#tab-panel-3194)
* [ Old dashboard ](#tab-panel-3195)
1. In the Cloudflare dashboard, go to the **Security Settings** page.
[ Go to **Settings** ](https://dash.cloudflare.com/?to=/:account/:zone/security/settings)
2. Filter by **Bot traffic**.
3. Go to **AI Labyrinth**.
4. Turn **AI Labyrinth** on.
1. Log in to the [Cloudflare dashboard ↗](https://dash.cloudflare.com/), and select your account and domain.
2. Go to **Security** \> **Bots**.
3. Select **Configure Bot Fight Mode**.
4. Enable **AI Labyrinth**.
```json
{"@context":"https://schema.org","@type":"BreadcrumbList","itemListElement":[{"@type":"ListItem","position":1,"item":{"@id":"/directory/","name":"Directory"}},{"@type":"ListItem","position":2,"item":{"@id":"/bots/","name":"Bots"}},{"@type":"ListItem","position":3,"item":{"@id":"/bots/additional-configurations/","name":"Additional configurations"}},{"@type":"ListItem","position":4,"item":{"@id":"/bots/additional-configurations/ai-labyrinth/","name":"AI Labyrinth"}}]}
```
---
---
title: Block AI Bots
description: You can choose to block AI bots by activating Block AI bots. Activating this setting will block verified bots that are classified as AI crawlers, as well as a number of unverified bots that behave similarly.
image: https://developers.cloudflare.com/core-services-preview.png
---
[Skip to content](#%5Ftop)
### Tags
[ AI ](https://developers.cloudflare.com/search/?tags=AI)
Was this helpful?
YesNo
[ Edit page ](https://github.com/cloudflare/cloudflare-docs/edit/production/src/content/docs/bots/additional-configurations/block-ai-bots.mdx) [ Report issue ](https://github.com/cloudflare/cloudflare-docs/issues/new/choose)
Copy page
# Block AI Bots
Block AI bots availability
The **Block AI bots** feature is only available in the new [application security dashboard](https://developers.cloudflare.com/security/).
You can choose to block AI bots by activating **Block AI bots**. Activating this setting will block [verified bots](https://developers.cloudflare.com/bots/concepts/bot/verified-bots/) that are classified as AI crawlers, as well as a number of unverified bots that behave similarly.
To block [AI bots](https://developers.cloudflare.com/bots/concepts/bot/#ai-bots):
1. In the Cloudflare dashboard, go to the **Security Settings** page.
[ Go to **Settings** ](https://dash.cloudflare.com/?to=/:account/:zone/security/settings)
2. Filter by **Bot traffic**.
3. Go to **Block AI bots**.
4. Under **Configurations**, select the edit icon. Choose from:
* **Only block on hostnames with ads**: Use this option if you wish to block AI bots only on portions of your site that show ads. Cloudflare automatically detects whether ads are present on a subdomain, and only block on hostnames that contain those ad units.
* **Block on all pages**: Use this option if you wish to block AI bots on all your pages.
* **Do not block (off)**: Use this option if you wish to allow AI bots on all your pages.
5. Select **Save** to save your configuration.
To block individual AI crawlers (rather than blocking all crawlers), use [AI Crawl Control](https://developers.cloudflare.com/ai-crawl-control/).
```json
{"@context":"https://schema.org","@type":"BreadcrumbList","itemListElement":[{"@type":"ListItem","position":1,"item":{"@id":"/directory/","name":"Directory"}},{"@type":"ListItem","position":2,"item":{"@id":"/bots/","name":"Bots"}},{"@type":"ListItem","position":3,"item":{"@id":"/bots/additional-configurations/","name":"Additional configurations"}},{"@type":"ListItem","position":4,"item":{"@id":"/bots/additional-configurations/block-ai-bots/","name":"Block AI Bots"}}]}
```
---
---
title: Custom rules
description: Understand when to use the built-in bot protection settings in Security Settings versus creating WAF custom rules for bot management.
image: https://developers.cloudflare.com/core-services-preview.png
---
[Skip to content](#%5Ftop)
Was this helpful?
YesNo
[ Edit page ](https://github.com/cloudflare/cloudflare-docs/edit/production/src/content/docs/bots/additional-configurations/custom-rules.mdx) [ Report issue ](https://github.com/cloudflare/cloudflare-docs/issues/new/choose)
Copy page
# Custom rules
Bot protection on Cloudflare works through two complementary mechanisms: built-in settings configured through toggles in **Security Settings**, and [WAF custom rules](https://developers.cloudflare.com/waf/custom-rules/) that you write using [bot management fields](https://developers.cloudflare.com/bots/reference/bot-management-variables/). Understanding when to use each approach helps you avoid creating duplicate rules and simplifies your security configuration.
The following features are configured through toggles and dropdowns in [Security Settings](https://developers.cloudflare.com/security/settings/). They do not require you to write any rule expressions.
| Feature | What it does | Availability |
| ----------------------------------------------------------------------------------------------------------------------- | ---------------------------------------------------------------------------------------------------------------- | ----------------------------- |
| [Block AI bots](https://developers.cloudflare.com/bots/additional-configurations/block-ai-bots/) | Blocks AI crawlers (GPTBot, ClaudeBot, Bytespider, and others) using an auto-updating managed rule | All plans |
| [AI Labyrinth](https://developers.cloudflare.com/bots/additional-configurations/ai-labyrinth/) | Feeds non-compliant AI crawlers into a maze of generated content | All plans |
| [Managed robots.txt](https://developers.cloudflare.com/bots/additional-configurations/managed-robots-txt/) | Prepends AI crawler disallow directives to your robots.txt | All plans |
| Super Bot Fight Mode > **Definitely automated** | Blocks or challenges traffic with a [bot score](https://developers.cloudflare.com/bots/concepts/bot-score/) of 1 | Pro, Business, Enterprise |
| Super Bot Fight Mode > **Likely automated** | Blocks or challenges traffic with a bot score of 2-29 | Business, Enterprise |
| [Verified bots](https://developers.cloudflare.com/bots/concepts/bot/verified-bots/) | Managed category of high-trust bots (Googlebot, Bingbot, and others) | Pro, Business, Enterprise |
| [Static resource protection](https://developers.cloudflare.com/bots/additional-configurations/static-resources/) | Extends bot actions to cover static file types | Pro, Business, Enterprise |
| [Optimize for WordPress](https://developers.cloudflare.com/bots/troubleshooting/wordpress-loopback-issue/) | Allows WordPress loopback requests through bot protection | Pro, Business, Enterprise |
| [JavaScript detections](https://developers.cloudflare.com/cloudflare-challenges/challenge-types/javascript-detections/) | Injects a lightweight script to identify clients that cannot execute JavaScript | All plans (automatic on Free) |
Bot settings update automatically as Cloudflare identifies new bot signatures and AI crawlers, while custom rules require manual updates. They do not count toward your [custom rule limits](https://developers.cloudflare.com/waf/custom-rules/#availability), and apply uniformly across your domain without the risk of expression errors.
## Custom rules use cases
Custom rules are valuable when you need capabilities that built-in settings do not offer. The following scenarios require [WAF custom rules](https://developers.cloudflare.com/waf/custom-rules/) with [bot management fields](https://developers.cloudflare.com/bots/reference/bot-management-variables/). Bot management fields are available to customers with a [Bot Management](https://developers.cloudflare.com/bots/get-started/bot-management/) subscription.
### Path-specific protection
Since Bot settings apply to all traffic across your domain, you may need an alternative approach to bot handling for different paths using custom rules — for example, stricter protection on `/login/` than on `/public/`.
#### Example
Block likely automated traffic only on your login endpoint:
```
(cf.bot_management.score lt 30 and not cf.bot_management.verified_bot and http.request.uri.path eq "/login")
```
### Custom score thresholds
The **Definitely automated** and **Likely automated** settings in Super Bot Fight Mode use fixed bot score groupings (1 and 2-29). If you need a different threshold, for example, challenging all traffic with a score below 20, you need a custom rule.
### Conditional logic
If you need to combine bot score with other request fields, such as country, ASN, URI path, JA3/JA4 fingerprint, or user agent, you need custom rules. Bot settings do not support compound conditions.
#### Example
Challenge likely automated traffic only from specific ASNs:
```
(cf.bot_management.score lt 30 and not cf.bot_management.verified_bot and ip.src.asnum in {64496 65536})
```
### Custom actions
Bot settings offer **Block**, **Managed Challenge**, and **Allow** as actions.
If you need other actions, such as **Log** (for testing rules before enforcement), **Interactive Challenge**, or **Skip** (to bypass other rules), you need custom rules.
### Detection ID targeting
To act on specific bot heuristic detections, such as [account takeover](https://developers.cloudflare.com/bots/additional-configurations/detection-ids/account-takeover-detections/) or [scraping](https://developers.cloudflare.com/bots/additional-configurations/detection-ids/scraping-detections/) patterns, you need custom rules using the `cf.bot_management.detection_ids` field. Bot settings do not expose individual detection IDs.
### Forwarding bot data to origin
To send bot scores, verified bot status, or JA3/JA4 fingerprints to your origin server, use [Transform Rules](https://developers.cloudflare.com/rules/transform/) (including [Managed Transforms](https://developers.cloudflare.com/rules/transform/managed-transforms/)) or [Snippets](https://developers.cloudflare.com/rules/snippets/). These are not part of the built-in bot settings.
## Execution order
Custom rules execute before Super Bot Fight Mode managed rules. If a custom rule takes a terminating action (such as _Block_ or _Managed Challenge_), the request does not reach bot settings.
Refer to [Security features interoperability](https://developers.cloudflare.com/waf/feature-interoperability/) for more information.
```json
{"@context":"https://schema.org","@type":"BreadcrumbList","itemListElement":[{"@type":"ListItem","position":1,"item":{"@id":"/directory/","name":"Directory"}},{"@type":"ListItem","position":2,"item":{"@id":"/bots/","name":"Bots"}},{"@type":"ListItem","position":3,"item":{"@id":"/bots/additional-configurations/","name":"Additional configurations"}},{"@type":"ListItem","position":4,"item":{"@id":"/bots/additional-configurations/custom-rules/","name":"Custom rules"}}]}
```
---
---
title: Detection IDs
description: Detection IDs are static rules used to detect predictable bot behavior with no overlap with human traffic. Detection IDs refer to the precise detection used to identify a bot, which could be from heuristics, verified bot detections, or anomaly detections. For example, a detection ID can identify if you sent your headers in a different order than what was expected of your browser.
image: https://developers.cloudflare.com/core-services-preview.png
---
[Skip to content](#%5Ftop)
Was this helpful?
YesNo
[ Edit page ](https://github.com/cloudflare/cloudflare-docs/edit/production/src/content/docs/bots/additional-configurations/detection-ids/index.mdx) [ Report issue ](https://github.com/cloudflare/cloudflare-docs/issues/new/choose)
Copy page
# Detection IDs
Detection IDs are static rules used to detect predictable bot behavior with no overlap with human traffic. Detection IDs refer to the precise [detection](https://developers.cloudflare.com/bots/concepts/bot-detection-engines/) used to identify a bot, which could be from heuristics, verified bot detections, or anomaly detections. For example, a detection ID can identify if you sent your headers in a different order than what was expected of your browser.
If you are having an issue with one of our heuristics, detection IDs allow you to decide which heuristics to enforce on your zones using customer configurable heuristics. You can choose unique actions for different bots, detected through Cloudflare’s heuristics engine. You can block, allow, or serve alternate content to specific bots to meet the unique needs of your site’s traffic.
Note
A request can trigger multiple detection IDs.
You can use `cf.bot_management.detection_ids` fields in tools such as:
* [Custom rules](https://developers.cloudflare.com/waf/custom-rules/)
* [Advanced Rate Limiting](https://developers.cloudflare.com/waf/rate-limiting-rules/)
* [Transform Rules](https://developers.cloudflare.com/rules/transform/)
* [Workers](https://developers.cloudflare.com/workers/) (as `request.cf.botManagement.detectionIds`)
Bot Detection IDs and tags are also available in [Bot Analytics](https://developers.cloudflare.com/bots/bot-analytics/) and [Security Analytics](https://developers.cloudflare.com/waf/analytics/security-analytics/).
Beta detections
Cloudflare may occasionally try beta detections as we continuously improve our detections.
It is possible, but uncommon, for you to have beta detection IDs on the Cloudflare dashboard that are not actively collecting data on your zone.
---
## Detection tags
Detection tags refer to the category associated with the detection ID at the time that Cloudflare has fingerprinted a bot. For example, if a detection tag is `go`, this means that Cloudflare has observed traffic from that detection ID from a Go programming language bot.
Note
Detection tags are available in Security Analytics, but not in the Security Events.
---
## Create or edit an expression
* [ New dashboard ](#tab-panel-3196)
* [ Old dashboard ](#tab-panel-3197)
1. In the Cloudflare dashboard, go to the **Security Analytics** page.
[ Go to **Analytics** ](https://dash.cloudflare.com/?to=/:account/:zone/security/analytics)
2. Apply filters and select **Create custom security rule** to create a custom rule based on your filters.
Alternatively, if you have already created a custom rule, you can go to the existing rule in **Security rules** and edit the expression based on your filters.
[ Go to **Security rules** ](https://dash.cloudflare.com/?to=/:account/:zone/security/security-rules)
3. Use the `cf.bot_management.detection_ids` field in the rule expression.
4. Select **Deploy**.
1. Log in to the [Cloudflare dashboard ↗](https://dash.cloudflare.com/), and select your account and domain.
2. Go to **Security** \> **Bots**, apply filters and select **Create custom rule** to create a [custom rule](https://developers.cloudflare.com/waf/custom-rules/create-dashboard/) based on those filters. Alternatively, if you already created a custom rule, go to **Security** \> **WAF** \> **Custom rules** and edit the expression of an existing custom rule.
3. Use the `cf.bot_management.detection_ids` field in the rule expression.
4. Select **Save**.
---
## Use cases
### Block requests that match a specific detection ID
JavaScript
```
any(cf.bot_management.detection_ids[*] eq 3355446)
and not cf.bot_management.verified_bot
and http.request.uri.path eq "/login"
and http.request.method eq "POST"
```
### Run Bot Management without specific detection IDs
JavaScript
```
cf.bot_management.score lt 30
and not cf.bot_management.verified_bot
and http.request.uri.path eq "/login"
and http.request.method eq "POST"
and not any(cf.bot_management.detection_ids[*] in {3355446 12577893})
```
---
## Bot Detection IDs via Logpush
You can create or edit existing Logpush jobs to include the new Bot Detection IDs field which will provide an array of IDs for each request that has heuristics match on it. The `BotDetectionIDs` field is available as part of the HTTP Requests dataset and you can add it to new or existing jobs via the Logpush API or on the Cloudflare dashboard. This is the primary method to discover Detection IDs.
* [ Dashboard ](#tab-panel-3198)
* [ API ](#tab-panel-3199)
1. In the Cloudflare dashboard, go to the **Logpush** page.
[ Go to **Logpush** ](https://dash.cloudflare.com/?to=/:account/logs)
2. Select **Create a Logpush Job**.
3. Select and enter the destination information.
4. Select **HTTP Requests** as the dataset.
5. Select **BotDetectionIDs** under the General data field category.
6. Prove the ownership.
7. Select **Save**.
[Update your logpush job](https://developers.cloudflare.com/logs/logpush/logpush-job/log-output-options/) by adding `BotDetectionIDs` to the `output_options:` parameters.
---
## Availability
Detection IDs are available for Enterprise Bot Management customers.
```json
{"@context":"https://schema.org","@type":"BreadcrumbList","itemListElement":[{"@type":"ListItem","position":1,"item":{"@id":"/directory/","name":"Directory"}},{"@type":"ListItem","position":2,"item":{"@id":"/bots/","name":"Bots"}},{"@type":"ListItem","position":3,"item":{"@id":"/bots/additional-configurations/","name":"Additional configurations"}},{"@type":"ListItem","position":4,"item":{"@id":"/bots/additional-configurations/detection-ids/","name":"Detection IDs"}}]}
```
---
---
title: Account takeover detections
description: Using the detection IDs below, you can detect and mitigate account takeover attacks. You can monitor the number of login requests for a given software and network combination, as well as the percentage of login errors. When it reaches a suspicious level, you can prevent these attacks by using custom rules, rate limiting rules, and Workers.
image: https://developers.cloudflare.com/core-services-preview.png
---
[Skip to content](#%5Ftop)
Was this helpful?
YesNo
[ Edit page ](https://github.com/cloudflare/cloudflare-docs/edit/production/src/content/docs/bots/additional-configurations/detection-ids/account-takeover-detections.mdx) [ Report issue ](https://github.com/cloudflare/cloudflare-docs/issues/new/choose)
Copy page
# Account takeover detections
Using the detection IDs below, you can detect and mitigate account takeover attacks. You can monitor the number of login requests for a given software and network combination, as well as the percentage of login errors. When it reaches a suspicious level, you can prevent these attacks by using [custom rules](https://developers.cloudflare.com/waf/custom-rules/), [rate limiting rules](https://developers.cloudflare.com/waf/rate-limiting-rules/), and [Workers](https://developers.cloudflare.com/workers/).
| Detection ID | Description |
| ------------ | ---------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------- |
| 201326592 | Matches traffic that is making a suspicious amount of login failures to the zone. |
| 201326593 | Matches traffic that is making a suspicious amount of login attempts to the zone. |
| 201326598 | Sets a dynamic threshold based on the normal traffic that is unique to the zone. When the ID matches a login failure, Bot Management sets the [bot score](https://developers.cloudflare.com/bots/concepts/bot-score/) to 29 and uses [anomaly detection](https://developers.cloudflare.com/bots/concepts/bot-detection-engines/#anomaly-detection-enterprise) as its score source. |
Login endpoints
Not all login endpoints are automatically detected.
Cloudflare evaluates and automatically detects your website or application's login endpoint, but non-traditional login endpoints may not be recognized.
For example, if you have a non-traditional login endpoint, you should label it with `cf-log-in` using the [endpoint labeling service](https://developers.cloudflare.com/api-shield/management-and-monitoring/endpoint-labels/). Once you have applied the `cf-log-in` label, Cloudflare will use the labeled endpoint for account takeover detection decisions.
## Challenges for account takeover detections
Cloudflare's [Managed Challenge](https://developers.cloudflare.com/cloudflare-challenges/challenge-types/challenge-pages/#managed-challenge) can limit brute-force attacks on your login endpoints.
To access account takeover detections:
* [ New dashboard ](#tab-panel-3200)
* [ Old dashboard ](#tab-panel-3201)
1. In the Cloudflare dashboard, go to the **Security rules** page.
[ Go to **Security rules** ](https://dash.cloudflare.com/?to=/:account/:zone/security/security-rules)
2. Select **Create rule** and choose **Custom rule**.
3. Fill out the form using **Bot Detection IDs** along with other necessary information.
4. Select **Save as draft** to return to the rule later, or **Deploy** to deploy the rule.
1. Log in to the [Cloudflare dashboard ↗](https://dash.cloudflare.com/), and select your account and domain.
2. Go to **Security** \> **WAF**.
3. Under **Custom rules**, select **Create rule**.
4. Fill out the form using **Bot Detection IDs** along with other necessary information.
5. Select **Save as draft** to return to the rule later, or **Deploy** to deploy the rule.
Rule example
```
(any(cf.bot_management.detection_ids[*] eq 201326593))
```
## Limit logins with account takeover detections
Rate limiting rules can limit the number of logins from a particular IP, JA4 fingerprint, or country.
To use rate limiting rules with account takeover detections:
* [ New dashboard ](#tab-panel-3202)
* [ Old dashboard ](#tab-panel-3203)
1. In the Cloudflare dashboard, go to the **Security rules** page.
[ Go to **Security rules** ](https://dash.cloudflare.com/?to=/:account/:zone/security/security-rules)
2. Select **Create rule** and choose **Rate limiting rule**.
3. Fill out the form using the **Custom expression builder** and `cf.bot_management_detection_ids` along with other necessary information.
4. Select **Save as draft** to return to the rule later, or **Deploy** to deploy the rule.
1. Log in to the [Cloudflare dashboard ↗](https://dash.cloudflare.com/), and select your account and domain.
2. Go to **Security** \> **WAF**.
3. Under **Rate limiting rules**, select **Create rule**.
4. Fill out the form using the **Custom expression builder** and `cf.bot_management_detection_ids` along with other necessary information.
5. Select **Save as draft** to return to the rule later, or **Deploy** to deploy the rule.
Enhanced with leaked credential detections
The rule can be enhanced with Leaked Credential Checks. Refer to the [WAF documentation](https://developers.cloudflare.com/waf/detections/leaked-credentials/) for more information on how to include leaked credentials and account takeover detections in a rate limiting rule.
```json
{"@context":"https://schema.org","@type":"BreadcrumbList","itemListElement":[{"@type":"ListItem","position":1,"item":{"@id":"/directory/","name":"Directory"}},{"@type":"ListItem","position":2,"item":{"@id":"/bots/","name":"Bots"}},{"@type":"ListItem","position":3,"item":{"@id":"/bots/additional-configurations/","name":"Additional configurations"}},{"@type":"ListItem","position":4,"item":{"@id":"/bots/additional-configurations/detection-ids/","name":"Detection IDs"}},{"@type":"ListItem","position":5,"item":{"@id":"/bots/additional-configurations/detection-ids/account-takeover-detections/","name":"Account takeover detections"}}]}
```
---
---
title: Additional detections
description: Cloudflare bot detection includes additional signals to catch different kinds of automated traffic.
image: https://developers.cloudflare.com/core-services-preview.png
---
[Skip to content](#%5Ftop)
Was this helpful?
YesNo
[ Edit page ](https://github.com/cloudflare/cloudflare-docs/edit/production/src/content/docs/bots/additional-configurations/detection-ids/additional-detections.mdx) [ Report issue ](https://github.com/cloudflare/cloudflare-docs/issues/new/choose)
Copy page
# Additional detections
Cloudflare bot detection includes additional signals to catch different kinds of automated traffic.
Bot management customers automatically benefit from the residential proxy detection improvement below, which lowers the [bot score](https://developers.cloudflare.com/bots/concepts/bot-score/) for matched requests. Using the detection ID in [custom rules](https://developers.cloudflare.com/waf/custom-rules/) provides even more visibility and control over mitigating residential proxy traffic.
| Detection ID | Description |
| ------------ | -------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------- |
| 50331651 | Observes traffic from residential proxy networks and similar commercial proxies. When the ID matches a request, Bot Management sets the bot score to 29 and uses [anomaly detection](https://developers.cloudflare.com/bots/concepts/bot-detection-engines/#anomaly-detection-enterprise) as its score source. |
```json
{"@context":"https://schema.org","@type":"BreadcrumbList","itemListElement":[{"@type":"ListItem","position":1,"item":{"@id":"/directory/","name":"Directory"}},{"@type":"ListItem","position":2,"item":{"@id":"/bots/","name":"Bots"}},{"@type":"ListItem","position":3,"item":{"@id":"/bots/additional-configurations/","name":"Additional configurations"}},{"@type":"ListItem","position":4,"item":{"@id":"/bots/additional-configurations/detection-ids/","name":"Detection IDs"}},{"@type":"ListItem","position":5,"item":{"@id":"/bots/additional-configurations/detection-ids/additional-detections/","name":"Additional detections"}}]}
```
---
---
title: Scraping detections
description: Scraping behavioral detection IDs allow you to better protect your website from volumetric scraping attacks by identifying anomalous behavior. The detection IDs below are specifically designed to catch suspicious scraping activity at the zone level.
image: https://developers.cloudflare.com/core-services-preview.png
---
[Skip to content](#%5Ftop)
Was this helpful?
YesNo
[ Edit page ](https://github.com/cloudflare/cloudflare-docs/edit/production/src/content/docs/bots/additional-configurations/detection-ids/scraping-detections.mdx) [ Report issue ](https://github.com/cloudflare/cloudflare-docs/issues/new/choose)
Copy page
# Scraping detections
Scraping behavioral detection IDs allow you to better protect your website from volumetric scraping attacks by identifying anomalous behavior. The detection IDs below are specifically designed to catch suspicious scraping activity at the zone level.
| Detection ID | Description |
| ------------ | --------------------------------------------------------------------------------------------------- |
| 50331648 | Observes patterns of requests sent to your zone, dynamically analyzing behavior by ASN. |
| 50331649 | Observes patterns of requests sent to your zone, dynamically analyzing behavior by JA4 fingerprint. |
## Challenges for scraping detections
Cloudflare's [Managed Challenge](https://developers.cloudflare.com/cloudflare-challenges/challenge-types/challenge-pages/#managed-challenge) can limit scraping attacks on your website.
To access scraping detections:
* [ New dashboard ](#tab-panel-3204)
* [ Old dashboard ](#tab-panel-3205)
1. In the Cloudflare dashboard, go to the **Security rules** page.
[ Go to **Security rules** ](https://dash.cloudflare.com/?to=/:account/:zone/security/security-rules)
2. Select **Create rule** and choose **Custom rule**.
3. Fill out the form using **Bot Detection IDs** along with other necessary information.
4. Select **Save as draft** to return to the rule later, or **Deploy** to deploy the rule.
1. Log in to the [Cloudflare dashboard ↗](https://dash.cloudflare.com/), and select your account and domain.
2. Go to **Security** \> **WAF**.
3. Under **Custom rules**, select **Create rule**.
4. Fill out the form using **Bot Detection IDs** along with other necessary information.
5. Select **Save as draft** to return to the rule later, or **Deploy** to deploy the rule.
Rule example
```
(any(cf.bot_management.detection_ids[*] in {50331648 50331649}) and not cf.bot_management.verified_bot)
```
Best practice
If you are choosing to challenge as your rule action, ensure that you exclude any API calls on which you do not want to issue a challenge. To exclude requests to such paths, edit the [WAF custom rule](https://developers.cloudflare.com/waf/custom-rules/) to exclude the relevant paths.
Note
The matched traffic for detection IDs `50331648` and `50331649` is dynamically re-calculated, meaning a single fingerprint would not be permanently flagged unless it continues to behave suspiciously at all times.
```json
{"@context":"https://schema.org","@type":"BreadcrumbList","itemListElement":[{"@type":"ListItem","position":1,"item":{"@id":"/directory/","name":"Directory"}},{"@type":"ListItem","position":2,"item":{"@id":"/bots/","name":"Bots"}},{"@type":"ListItem","position":3,"item":{"@id":"/bots/additional-configurations/","name":"Additional configurations"}},{"@type":"ListItem","position":4,"item":{"@id":"/bots/additional-configurations/detection-ids/","name":"Detection IDs"}},{"@type":"ListItem","position":5,"item":{"@id":"/bots/additional-configurations/detection-ids/scraping-detections/","name":"Scraping detections"}}]}
```
---
---
title: JA3/JA4 fingerprint
description: JA3 and JA4 fingerprints help you profile specific SSL/TLS clients across different destination IPs, Ports, and X509 certificates.
image: https://developers.cloudflare.com/core-services-preview.png
---
[Skip to content](#%5Ftop)
Was this helpful?
YesNo
[ Edit page ](https://github.com/cloudflare/cloudflare-docs/edit/production/src/content/docs/bots/additional-configurations/ja3-ja4-fingerprint/index.mdx) [ Report issue ](https://github.com/cloudflare/cloudflare-docs/issues/new/choose)
Copy page
# JA3/JA4 fingerprint
[**JA3** ↗](https://github.com/salesforce/ja3) and [**JA4** ↗](https://github.com/FoxIO-LLC/ja4) **fingerprints** help you profile specific SSL/TLS clients across different destination IPs, Ports, and X509 certificates.
JA4 fingerprint adds new functionality by sorting ClientHello extensions and reducing the total number of unique fingerprints for modern browsers.
Note
JA3 and JA4 fingerprints are only available to Enterprise customers who have purchased Bot Management.
If you want to use JA4 fingerprints and Signals Intelligence, your Workers script must be able to handle the absence of any field in the array, including:
* The possibility that the JA4 fingerprint could be missing.
* The possibility that the `ja4Signals` array could be missing.
* Results with `NaN` or `Infinity` values will be excluded from the array.
```
{
"ja4Signals": {
"h2h3_ratio_1h": 0.98826485872269,
"heuristic_ratio_1h": 7.288895722013e-05,
"reqs_quantile_1h": 0.99905741214752,
"uas_rank_1h": 901,
"browser_ratio_1h": 0.93640440702438,
"paths_rank_1h": 655,
"reqs_rank_1h": 850,
"cache_ratio_1h": 0.18918327987194,
"ips_rank_1h": 662,
"ips_quantile_1h": 0.99926590919495
},
"jaSignalsParsed": {
"ratios": {
"h2h3_ratio_1h": 0.98826485872269,
"heuristic_ratio_1h": 7.288895722013e-05,
"browser_ratio_1h": 0.93640440702438,
"cache_ratio_1h": 0.18918327987194
},
"ranks": {
"uas_rank_1h": 901,
"paths_rank_1h": 655,
"reqs_rank_1h": 850,
"ips_rank_1h": 662
},
"quantiles": {
"reqs_quantile_1h": 0.99905741214752,
"ips_quantile_1h": 0.99926590919495
}
}
}
```
When JA4 Signals are missing, the output appears as follows:
```
{
"ja4Signals": {},
"jaSignalsParsed": {
"ratios": {},
"ranks": {},
"quantiles": {}
}
}
```
Note
This sample was generated using [Workers' Cloudflare Object script](https://developers.cloudflare.com/workers/examples/accessing-the-cloudflare-object/).
The JA3 or JA4 fingerprint is an SSL/TLS-based identifier and can be null or empty in logs under specific circumstances:
* Since JA3 and JA4 are calculated during the TLS (SSL) handshake, they will not be present for non-encrypted HTTP traffic.
* The field may be empty when a [Worker](https://developers.cloudflare.com/workers/) sends a request to a zone that is either internal to Cloudflare's network (O2O traffic that is not proxied) or to a third-party origin, or when a Worker is routing traffic to the target zone.
* The fingerprints may be absent when Bot Management itself is skipped for a request, as the feature is responsible for calculating and populating these values.
Generally, [O2O traffic](https://developers.cloudflare.com/cloudflare-for-platforms/cloudflare-for-saas/saas-customers/) should include JA3 or JA4 fingerprints unless a Worker is used to route traffic from the eyeball (client-facing) zone to the target zone.
## Analytics
To get more information about potential bot requests, use these JA3 and JA4 fingerprints in:
* [Bot Analytics](https://developers.cloudflare.com/bots/bot-analytics/#enterprise-bot-management)
* [Security Events](https://developers.cloudflare.com/waf/analytics/security-events/) and [Security Analytics](https://developers.cloudflare.com/waf/analytics/security-analytics/)
* [Analytics GraphQL API](https://developers.cloudflare.com/analytics/graphql-api/), specifically the **HTTP Requests** dataset
* [Logs](https://developers.cloudflare.com/logs/logpush/logpush-job/datasets/zone/http%5Frequests/)
## Actions
To adjust how your application responds to specific fingerprints, use them with:
* [WAF custom rules](https://developers.cloudflare.com/waf/custom-rules/)
* [Transform Rules](https://developers.cloudflare.com/rules/transform/)
* [Cloudflare Workers](https://developers.cloudflare.com/workers/runtime-apis/request/#incomingrequestcfproperties)
## Use cases
### Block or allow certain traffic
A group of similar requests may share the same JA3 fingerprint. For this reason, JA3 may be useful in blocking an incoming threat. For example, if you notice that a bot attack is not caught by existing defenses, create a [custom rule](https://developers.cloudflare.com/waf/custom-rules/) that blocks or challenges the JA3 used for the attack.
Alternatively, if existing defenses are blocking traffic that is actually legitimate, create a [custom rule](https://developers.cloudflare.com/waf/custom-rules/) with the _Skip_ action allowing the JA3 seen across good requests.
JA3 may also be useful if you want to immediately remedy false positives or false negatives with Bot Management.
### Allow mobile traffic
Often, mobile application traffic will produce the same JA3 fingerprint across devices and users. This means you can identify your mobile application traffic by its JA3 fingerprint.
Use the JA3 fingerprint to [allow traffic](https://developers.cloudflare.com/waf/custom-rules/use-cases/challenge-bad-bots/#adjust-for-mobile-traffic) from your mobile application, but block or challenge remaining traffic.
```json
{"@context":"https://schema.org","@type":"BreadcrumbList","itemListElement":[{"@type":"ListItem","position":1,"item":{"@id":"/directory/","name":"Directory"}},{"@type":"ListItem","position":2,"item":{"@id":"/bots/","name":"Bots"}},{"@type":"ListItem","position":3,"item":{"@id":"/bots/additional-configurations/","name":"Additional configurations"}},{"@type":"ListItem","position":4,"item":{"@id":"/bots/additional-configurations/ja3-ja4-fingerprint/","name":"JA3/JA4 fingerprint"}}]}
```
---
---
title: Signals Intelligence
description: For every available JA4 fingerprint, Bot Management customers can view how Cloudflare sees it on the Internet and what behavior we view with the fingerprint. This data can help you understand why a request is scored in a particular fashion or allow you to use the aggregate data in your own ML models, run in either Cloudflare Workers or at the origin location.
image: https://developers.cloudflare.com/core-services-preview.png
---
[Skip to content](#%5Ftop)
Was this helpful?
YesNo
[ Edit page ](https://github.com/cloudflare/cloudflare-docs/edit/production/src/content/docs/bots/additional-configurations/ja3-ja4-fingerprint/signals-intelligence.mdx) [ Report issue ](https://github.com/cloudflare/cloudflare-docs/issues/new/choose)
Copy page
# Signals Intelligence
For every available [JA4 fingerprint](https://developers.cloudflare.com/bots/additional-configurations/ja3-ja4-fingerprint/), Bot Management customers can view how Cloudflare sees it on the Internet and what behavior we view with the fingerprint. This data can help you understand why a request is scored in a particular fashion or allow you to use the aggregate data in your own ML models, run in either [Cloudflare Workers](https://developers.cloudflare.com/workers/) or at the origin location.
Specifically, for each JA4 fingerprint, you will be able to access the following information:
* The percentage of traffic associated with browsers that Cloudflare sees.
* The percentage of traffic associated with known bots that Cloudflare sees.
* The number of networks Cloudflare sees actively using this fingerprint.
* The number of Cloudflare sites that see traffic from this fingerprint.
* The frequency that fingerprint requests caches content and generates errors.
This data gives you access to insights only available via the Cloudflare network and generated by our unique edge network that sits behind 20% of all Internet traffic. Additionally, you can feed this data into your own [Workers AI](https://developers.cloudflare.com/workers-ai/)\-powered custom machine learning models via the Signals Intelligence fields below.
## Signals Intelligence fields
Signals Intelligence fields show observations about a particular JA4 that Cloudflare has seen globally over the last hour.
| Field name | Description |
| -------------------- | ------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------- |
| h2h3\_ratio\_1h | The ratio of HTTP/2 and HTTP/3 requests combined with the total number of requests for the JA4 fingerprint in the last hour. Higher values indicate a higher proportion of HTTP/2 and HTTP/3 requests compared to other protocol versions. |
| heuristic\_ratio\_1h | The ratio of requests with a scoreSrc value of "heuristics" for the JA4 fingerprint in the last hour. Higher values suggest a larger proportion of requests being flagged by heuristic-based scoring. |
| reqs\_quantile\_1h | The quantile position of the JA4 fingerprint based on the number of requests across all fingerprints in the last hour. Higher values indicate a relatively higher number of requests compared to other fingerprints. |
| uas\_rank\_1h | The rank of the JA4 fingerprint based on the number of distinct user agents across all fingerprints in the last hour. Lower values indicate a higher diversity of user agents associated with the fingerprint. |
| browser\_ratio\_1h | The ratio of requests originating from browser-based user agents for the JA4 fingerprint in the last hour. Higher values suggest a higher proportion of browser-based requests. |
| paths\_rank\_1h | The rank of the JA4 fingerprint based on the number of unique request paths across all fingerprints in the last hour. Lower values indicate a higher diversity of request paths associated with the fingerprint. |
| reqs\_rank\_1h | The rank of the JA4 fingerprint based on the number of requests across all fingerprints in the last hour. Lower values indicate a higher number of requests associated with the fingerprint. |
| cache\_ratio\_1h | The ratio of cacheable responses for the JA4 fingerprint in the last hour. Higher values suggest a higher proportion of responses that can be cached. |
| ips\_rank\_1h | The rank of the JA4 fingerprint based on the number of unique client IP addresses across all fingerprints in the last hour. Lower values indicate a higher number of distinct client IPs associated with the fingerprint. |
| ips\_quantile\_1h | The quantile position of the JA4 fingerprint based on the number of unique client IP addresses across all fingerprints in the last hour. Higher values indicate a relatively higher number of distinct client IPs compared to other fingerprints. |
If you want to use JA4 fingerprints and Signals Intelligence, your Workers script must be able to handle the absence of any field in the array, including:
* The possibility that the JA4 fingerprint could be missing.
* The possibility that the `ja4Signals` array could be missing.
* Results with `NaN` or `Infinity` values will be excluded from the array.
```json
{"@context":"https://schema.org","@type":"BreadcrumbList","itemListElement":[{"@type":"ListItem","position":1,"item":{"@id":"/directory/","name":"Directory"}},{"@type":"ListItem","position":2,"item":{"@id":"/bots/","name":"Bots"}},{"@type":"ListItem","position":3,"item":{"@id":"/bots/additional-configurations/","name":"Additional configurations"}},{"@type":"ListItem","position":4,"item":{"@id":"/bots/additional-configurations/ja3-ja4-fingerprint/","name":"JA3/JA4 fingerprint"}},{"@type":"ListItem","position":5,"item":{"@id":"/bots/additional-configurations/ja3-ja4-fingerprint/signals-intelligence/","name":"Signals Intelligence"}}]}
```
---
---
title: JavaScript Detections
description: JavaScript Detections is a type of challenge separate from Cloudflare’s Challenge Pages or Turnstile. Javascript Detections helps Cloudflare's bot solutions identify automated requests.
image: https://developers.cloudflare.com/core-services-preview.png
---
[Skip to content](#%5Ftop)
Was this helpful?
YesNo
[ Edit page ](https://github.com/cloudflare/cloudflare-docs/edit/production/src/content/docs/cloudflare-challenges/challenge-types/javascript-detections.mdx) [ Report issue ](https://github.com/cloudflare/cloudflare-docs/issues/new/choose)
Copy page
# JavaScript Detections
JavaScript Detections is a type of challenge separate from Cloudflare’s Challenge Pages or Turnstile. Javascript Detections helps Cloudflare's [bot solutions](https://developers.cloudflare.com/bots/) identify automated requests.
While Challenge Pages and Turnstile rely on client-side signals to determine the authenticity of a request, Bot Management’s JavaScript Detections relies on client-side signals and run on every single request made to your website.
## Process
JavaScript Detections is implemented on your website via a lightweight, invisible JavaScript code snippet that follows Cloudflare's [privacy standards ↗](https://www.cloudflare.com/privacypolicy/).
JavaScript is injected only in response to requests for HTML pages or page views, excluding AJAX calls. API and mobile application traffic is unaffected.
JavaScript Detections has a lifespan of 15 minutes. However, the code is injected again before the session expires. After page load, the script is deferred and utilizes a separate thread (where available) to ensure that performance impact is minimal. The snippets of JavaScript will contain a source pointing to the Challenge Platform, with paths that start with `/cdn-cgi/challenge-platform/…`
Once JavaScript Detections is injected on the HTML page, the visitor's browser will run the JavaScript code snippet and a `cf_clearance` cookie is issued to the visitor. The information in JavaScript Detections is stored in the `cf_clearance` cookie and is used to populate `js_detection.passed`.
* If the visitor is verified and a `cf_clearance` cookie is issued, it will contain the outcome: `cf.bot_management.js_detection.passed` \= `true`
* If the verification fails, the cookie will contain the outcome: `cf.bot_management.js_detection.passed` \= `false`
Note
The `cf_clearance` cookie cannot exceed the maximum size of 4096 bytes.
Warning
Enforcement against bots does **not** occur even if the cookie is flagged false.
You must enable JavaScript Detections and then create a custom WAF rule using the `cf.bot_management.js_detection.passed` field to block or challenge a failed request.
When the visitor encounters a WAF custom rule on your website, the rule will check the outcome of the `cf_clearance` cookie. The outcome of the `cf_clearance` cookie determines whether the request passes, or is blocked or challenged.
Refer to the steps below to enable and enforce JavaScript Detections.
## 1\. Enable JavaScript Detections
For Bot Fight Mode customers, [JavaScript Detections](https://developers.cloudflare.com/cloudflare-challenges/challenge-types/javascript-detections/) is automatically enabled and cannot be disabled.
For Super Bot Fight Mode and Bot Management for Enterprise customers, [JavaScript Detections](https://developers.cloudflare.com/cloudflare-challenges/challenge-types/javascript-detections/) is optional.
* [ New dashboard ](#tab-panel-3354)
* [ Old dashboard ](#tab-panel-3355)
1. In the Cloudflare dashboard, go to the **Security Settings** page.
[ Go to **Settings** ](https://dash.cloudflare.com/?to=/:account/:zone/security/settings)
2. Under your bot traffic plan configurations, select the edit icon for **JS detections** and turn **JavaScript Detections** on.
1. Log in to the [Cloudflare dashboard ↗](https://dash.cloudflare.com/), and select your account and domain.
2. Go to **Security** \> **Bots**.
3. Select **Configure Bot Management**.
4. For **JavaScript Detections**, switch the toggle to **On**.
For more details on how to set up bot protection, refer to the [Bots documentation](https://developers.cloudflare.com/bots/get-started/).
## 2\. Enforce execution of JavaScript Detections
Once you enable JavaScript detections, you must use the `cf.bot_management.js_detection.passed` field to create [WAF custom rules](https://developers.cloudflare.com/waf/custom-rules/) (or the `request.cf.botManagement.jsDetection.passed` variable in [Workers](https://developers.cloudflare.com/workers/)).
When adding this field to WAF custom rules, it is used on endpoints expecting browser traffic (avoiding native mobile applications or websocket endpoints), after a user's first request to your application (Cloudflare needs at least one HTML request before injecting JavaScript detection), and with the Managed Challenge action, because there are legitimate reasons a user might not have passed a JavaScript Detection challenge (network issues, ad blockers, disabled JavaScript in browser, native mobile applications).
### Prerequisites
* You must have an [Enterprise Bot Management](https://developers.cloudflare.com/bots/plans/bm-subscription/) subscription.
* You must have JavaScript Detections enabled on your zone.
* You must have [updated your Content Security Policy headers](https://developers.cloudflare.com/cloudflare-challenges/challenge-types/javascript-detections/#if-you-have-a-content-security-policy-csp) for JavaScript detections.
* You must not run this field on websocket endpoints.
* You must use the field in a custom rules expression that expects only browser traffic.
* The action should always be a managed challenge in case a legitimate user has not received the challenge for network or browser reasons.
* The path specified in the rule builder should never be the first HTML page a user visits when browsing your site.
The `cf.bot_management.js_detection.passed` field should never be used in a WAF custom rule that matches a visitor's first request to a site. It is necessary to have at least one HTML request before Cloudflare can inject JavaScript detection.
* [ WAF rule example ](#tab-panel-3352)
* [ Workers example ](#tab-panel-3353)
```
(http.request.uri.path eq "/api/v4/user/create" and http.request.method eq "POST" and not cf.bot_management.verified_bot)
and (cf.bot_management.score lt 30 or !cf.bot_management.js_detection.passed)
```
JavaScript
```
"botManagement": {
"jsDetection": {
"passed": false
}
}
```
Refer to the [WAF documentation](https://developers.cloudflare.com/waf/custom-rules/create-dashboard/) for more information on creating a custom rule.
## API
If you enable JavaScript Detections via the dashboard, Cloudflare will insert a script tag in all HTML pages served on your website. If you would prefer to limit where JavaScript Detections is served, you can do so with the JavaScript Detections API script.
The JavaScript Detections API allows you more granular control over when and where JavaScript Detections is injected on your website, as well as an option for callback handling (for logging or other additional actions).
You can explicitly add a script reference to `/cdn-cgi/challenge-platform/scripts/jsd/api.js` and your own code calling `window.cloudflare.jsd.executeOnce` on specific HTML pages of your website.
Warning
It is not recommended to combine both approaches (zone-wide toggle and the manual injection). If you want to selectively deploy JavaScript Detections only on certain pages, disable JavaScript Detections via the Cloudflare dashboard and use the JavaScript Detections API exclusively.
The following script must be added to every page that you wish to have JavaScript Detections enabled:
JavaScript
```